Microsoft Defender External Attack Surface Management
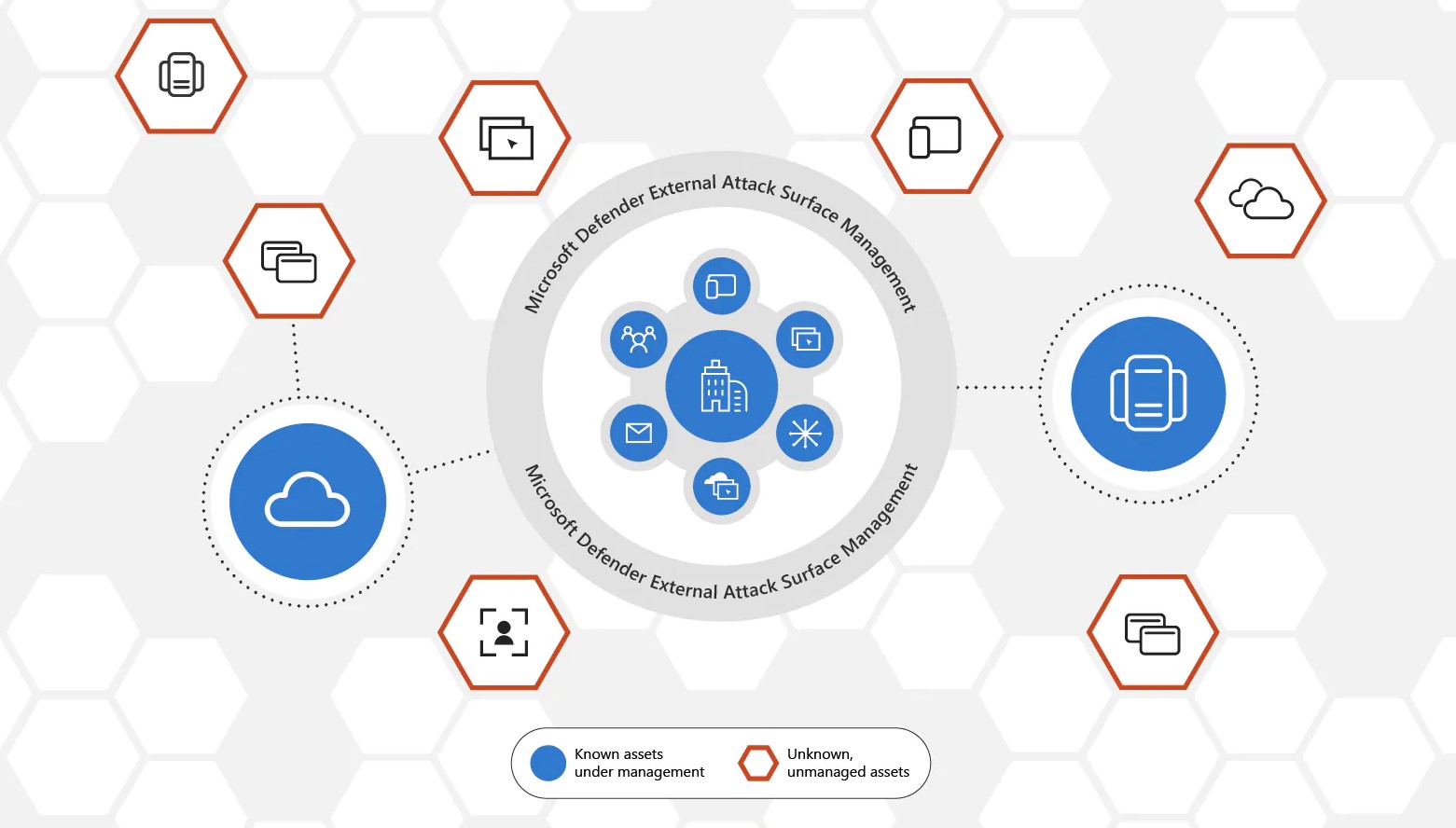
Microsoft Defender External Attack Surface Management (Defender EASM) continuously discovers and maps your digital attack surface to provide an external view of your online infrastructure. This visibility enables security and IT teams to identify unknowns, prioritize risk, eliminate threats, and extend vulnerability and exposure control beyond the firewall. Defender EASM leverages Microsoft’s crawling technology to discover assets that are related to your known online infrastructure, and actively scans these assets to discover new connections over time. Attack Surface Insights are generated by leveraging vulnerability and infrastructure data to showcase the key areas of concern for your organization.
What is the Microsoft Defender External Attack Surface Management service about?
Global attack surface discovery technology finds, analyzes, and categorizes external-facing resources as they appear
Dynamic inventory includes external assets across multiple cloud environments, including unknown resources like shadow IT
Deep insight into assets uncovers vulnerabilities and identifies emerging risks
Visibility into your external attack surface enhances Microsoft Defender for end-to-end cloud security
Souce: Microsoft
What will be provided with the Microsoft Defender External Attack Surface Management service?
The service provides you with a complete overview and hands-on experience with Microsoft Defender EASM to get Microsoft Defender EASM up and running in your environment. The service consists of the following deliverables:
Workshop: During the workshop, we provide you with an overview of Microsoft Defender External Attack Surface Management (EASM) so that you understand the prerequisites, features and real-world use-cases.
Initial Setup and Configuration: We support you with getting Microsoft Defender External Attack Surface Management (EASM) up and running in your environment.
Review – We assist you with the review of the initial findings made by Defender External Attack Surface Management (EASM).
Documentation: Microsoft Defender External Attack Surface Management (EASM) setup and configuration documentation
What are the key benefits of the Microsoft Defender External Attack Surface Management?
The most important benefits are the following:
Eliminate external security gaps – View your organization’s web applications, dependencies, and web infrastructure through a single pane of glass with a dynamic record system. Gain enhanced visibility to enable security and IT teams to identify previously unknown resources, prioritize risk, and eliminate threats.
Extend security beyond the firewall – View your rapidly changing global attack surface in real-time with complete visibility into your organization’s internet-exposed resources. A simple, searchable inventory provides network teams, security defenders, and incident responders with verified insights into vulnerabilities, risks, and exposures from hardware to individual application components.
Understand your security posture – Gain a holistic view of your security posture to develop best practices and make informed decisions about security control investments and remediation with a dynamic inventory of external resources across the internet and multiple cloud environments.



